Solution: Industrial Security Concepts | IEC 62443
Solution: Industrial Security Concepts | IEC 62443
Industrial security concepts for industrial automation systems according to IEC 62443
Security from one source
TÜV AUSTRIA accompanies companies on their way to certification according to IEC 62443 with comprehensive analyses & consulting services as well as support during implementation. Thanks to its holistic view of companies, TÜV AUSTRIA sometimes ensures ongoing risk minimisation, competitive advantages through independent third party verification as well as consistent safety.
Accreditation
Cyber Security: Risk analysis and management according to IEC 62443
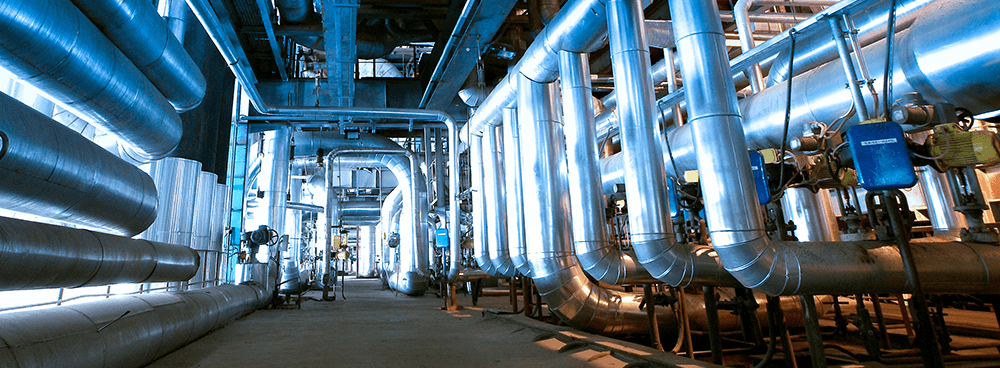
With the increasing connectivity of production plants (IIoT), new hazards arise that need to be included in traditional risk management processes. As a plant operator, machine or control manufacturer, you should also be aware of these risks. The IEC 62443 international standard series addresses the cyber security of Industrial Automation and Control Systems (IACS), taking a holistic approach that covers the entire lifecycle.
Cyber Security & IT/OT Integrity
Do I need it at all?
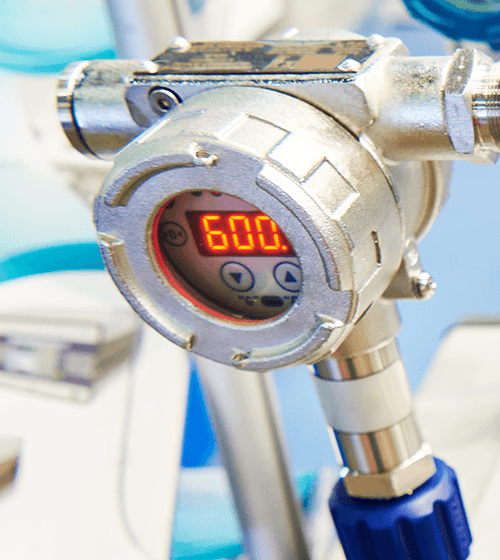
Example based on the TRITON malware framework: Triton, which was first discovered in 2017 in a Saudi Arabian chemical plant, is one of the best-known representatives of industrial plant-specific malware. In this case, the plant’s security system is specifically attacked in order to take over and control it remotely. At the time, the software had already been dormant in the system for several years before it caused the plant to fail twice in 2017. However, the attackers could also have triggered the release of dangerous gases or explosions, which would have endangered not only economic resources but also human lives.
Common cyber security myths
- Myth 1: We are not connected to the internet at all.
- Myth 2: Our firewall protects us from any dangers.
- Myth 3: Hackers have no idea about SCADA/DCS/PLC.
- Myth 4: Our system is not a target for attacks.
- Myth 5: Our security system will repel all damage.
Machine and plant operators
Thanks to the IEC 62443 standard, you as a machine/plant operator know the security requirements of your operation and are thus in a position to both secure your production and expand your operation with new machines or process plants that meet the security requirements without much additional measures (IEC 62443 3-2, 3-3).
Machine manufacturers and plant constructors
The IEC 62443 standard enables you as a plant and machine manufacturer to build and install systems with defined security requirements (IEC 62443 3-2, 3-3). This enables seamless integration into existing plants with known security requirements.
Controller manufacturer (IACS)
You as a controller manufacturer (IACS) can include the consideration of security requirements according to IEC 62443 4-1 in your product development processes in order to develop controllers with the security requirements relevant to your customers according to IEC 62443-4-2 IEC. Maintenance and service processes are made safe thanks to IEC 62443 2-4.
Plant Safety & Risk Management
Risk factors to which we should pay attention
Until about 15 years ago, plant performance and safety was based on technical integrity and processes and systems. At that time, it was recognised that human factors had a major impact on safety and performance. General risk management assumptions suggest that up to 80% of all safety and performance incidents are caused by human factors.
It is important to understand that cyber security integrity breaches can have a major impact on security and performance. Cyber security incidents can originate from human factors, systems and direct technical integrity.
TÜV AUSTRIA Services
Industrial plants
- Network segmentation – IT/OT
- Incident & Patch Management
- Vulnerability assessments & penetration tests
- Security awareness training for employees
IoT, IIoT and Industrial Automated Control Systems (IACS)
- Secure product development, integration and certification
- Security Hardening
- Secure hardware and software for the entire product life cycle
Physical & cognitive assistance systems
- Security by Design
- Collaborative Robotics and AR/VR
- Evaluation of the workspace
Overview of the IEC 62443 family
Part 1: General
- Part 1.1: Terms, concepts and models
- Part 1-2: List of terms and abbreviations
- Part 1-3: Measures of compliance with system safety
- Part 1-4: IACS Security Life Cycle and Use Cases
Part 2: Policies and procedures
- Part 2-1: Setting up an industrial automation and control system.
- Part 2-2: Guidance for the Implementation of an IACS Security Management System
- Part 2-3: Patch Management in the IACS Environment
- Part 2-4: Security Programme Requirement for IACS Service Providers
Part 3: System
- Part 3-1: Safety technologies for industrial automation and control systems
- Part 3-2: Safety risk assessment and system design
- Part 3-3: System requirements and safety levels
Part 4: Component / Product
- Part 4-1: Requirements for a safe product development cycle
- Part 4-2: Technical safety requirements for IACS components